One Engine. Every Fraud Type.
Your Infrastructure.
Real-time decisioning, ML scoring, and case management — deployed where your data lives. Built specifically for Southeast Asian banks and fintechs.
Pilot-stage · early access — manual approval within 1 business day
110
Pre-configured Rules
Across banking & e-commerce
47
Device Signals
Multi-vendor intelligence
7
Pipeline Stages
Real-time evaluation
3
Supervised Model Candidates
Offline training & shadow scoring
How It Works
Three steps from integration to protection. No months-long implementations.
Connect
Integrate via REST API or batch with your core banking system.
Configure
Choose from pre-built templates or create custom rules via the rules editor.
Protect
Real-time scoring, alerts, and case management from day one.
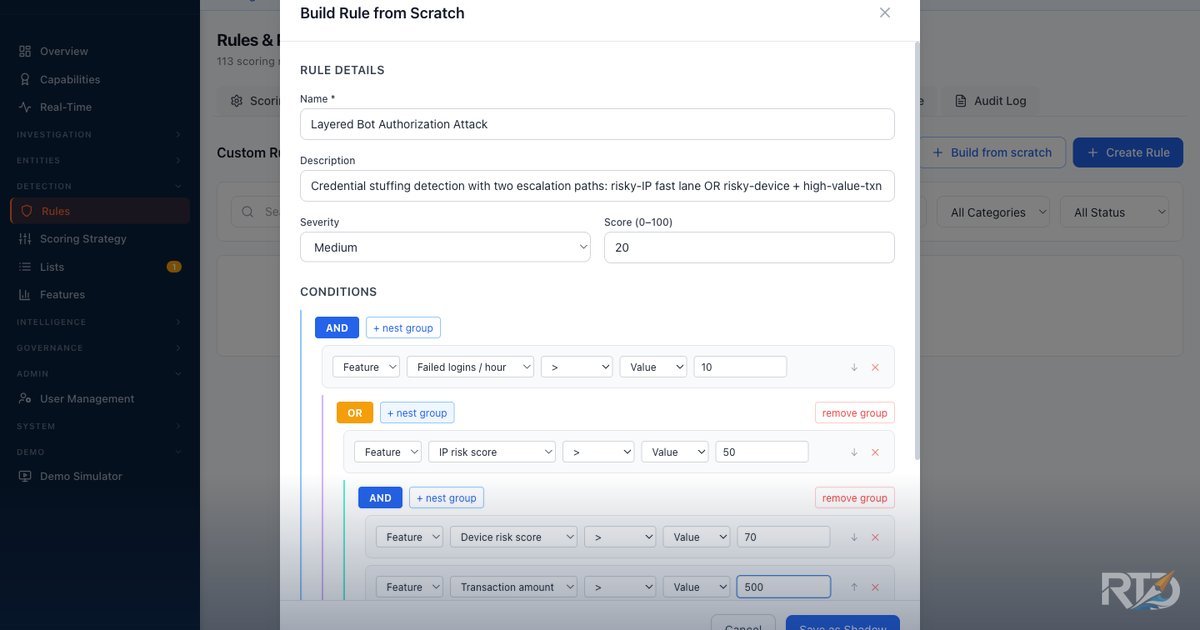
Rule Engine
110 pre-configured fraud detection templates across banking and e-commerce scenarios, plus a no-code rule builder that lets fraud analysts compose nested AND/OR logic — with a live pre-save backtest against real traffic and maker-checker approval enforced by code, not policy.
- Pre-configured fraud detection templates across 10 categories: wire, ACH, check, card, ATO, identity, money flow, cross-cut, device intelligence, and behavioral biometrics
- No-code rule builder — nested AND/OR composition with arbitrary depth, junctions flipped per group, and a plain-English preview that is the rule (no translation layer between UI and engine)
- Pre-save backtest against the last N hours of real traffic — see the exact count of historical transactions that would have matched, the match rate, and a sample of events, before the rule goes live
- Maker-checker enforced by code — the API blocks self-approval on the approval path itself (not just a permissions flag); every proposal, approval, and rejection writes to an immutable audit log
- A/B testing and shadow mode for safe rollout of new rules
- Complete audit trail for every rule change
Let fraud teams respond when the attack changes
The credential reset demo shows an analyst defining a new feature from recent reset, beneficiary, and transfer behavior, then using it in a reviewed rule without creating a parallel engineering workflow.
Create the signal: define a reusable feature with ownership, schema, and approval state.
Bind it to a rule: combine the new feature with existing platform signals in the rule builder.
Release with control: keep draft, review, and launch decisions visible to fraud and risk stakeholders.
Model Output
0.87
High Risk
ML Scoring & Explainability
Combine machine learning models with rule-based logic in a unified scoring pipeline. Every score comes with context your team can understand.
- Supervised offline training and shadow-scoring support
- SHAP-based explainability — per-prediction feature attribution
- Model versioning and lifecycle management
- Hybrid rule + ML scoring with per-flow weight control — independent weights per transaction type
- Candidate model comparison and benchmark reporting foundations
- Adaptive Confidence Engine — automated performance monitoring with weight adjustment recommendations Learn more
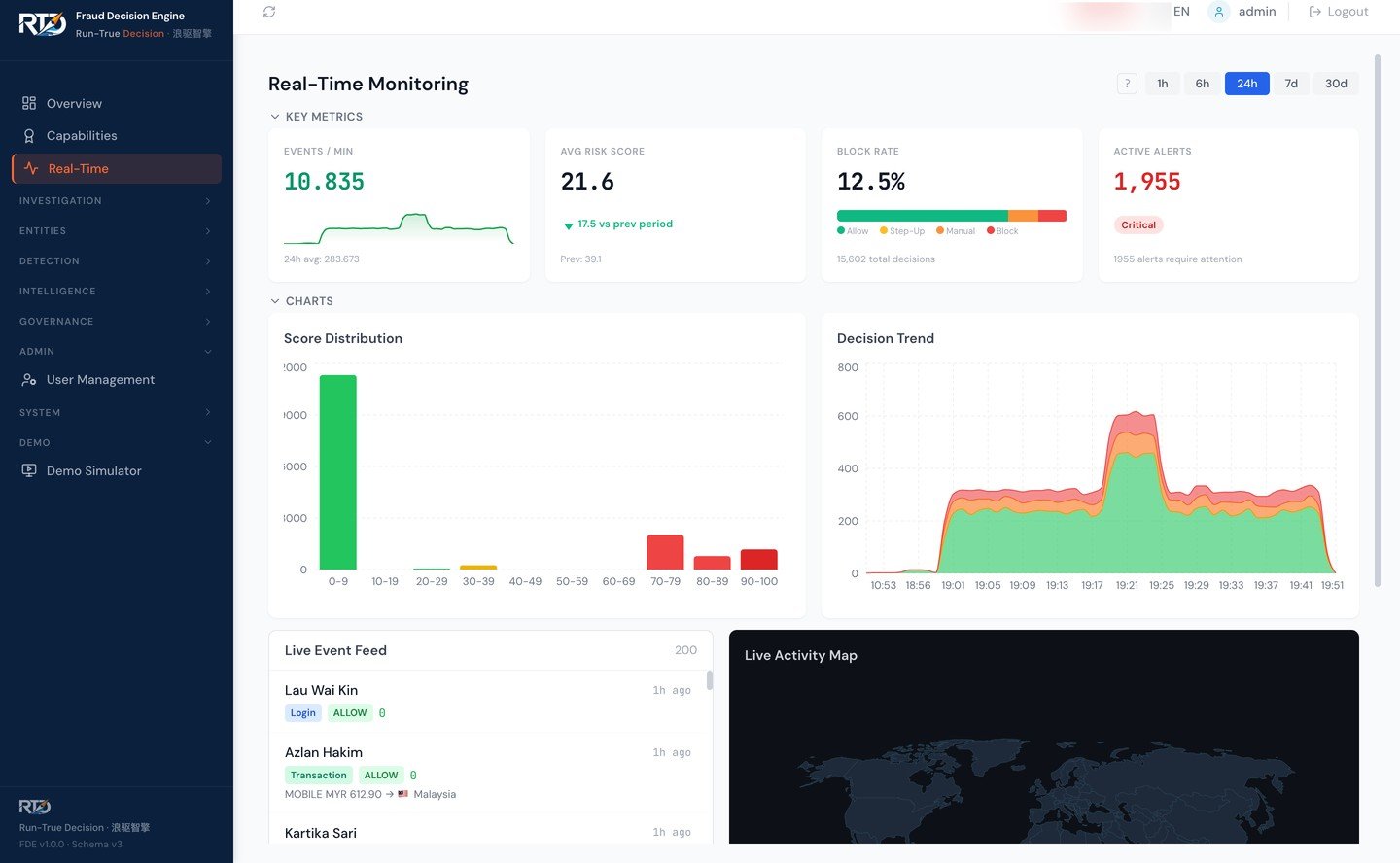
Real-Time Decisioning
Designed for millisecond-level response times. Every transaction gets an Allow, Step-Up, Manual Review, or Block decision through configurable workflows.
- Designed for millisecond-level response times
- Allow / Step-Up / Manual Review / Block decision outcomes
- API-first architecture for seamless integration
- Configurable decision workflows
- Priority queue management for high-value transactions
ALLOW
68%
STEP-UP
17%
REVIEW
9%
BLOCK
6%
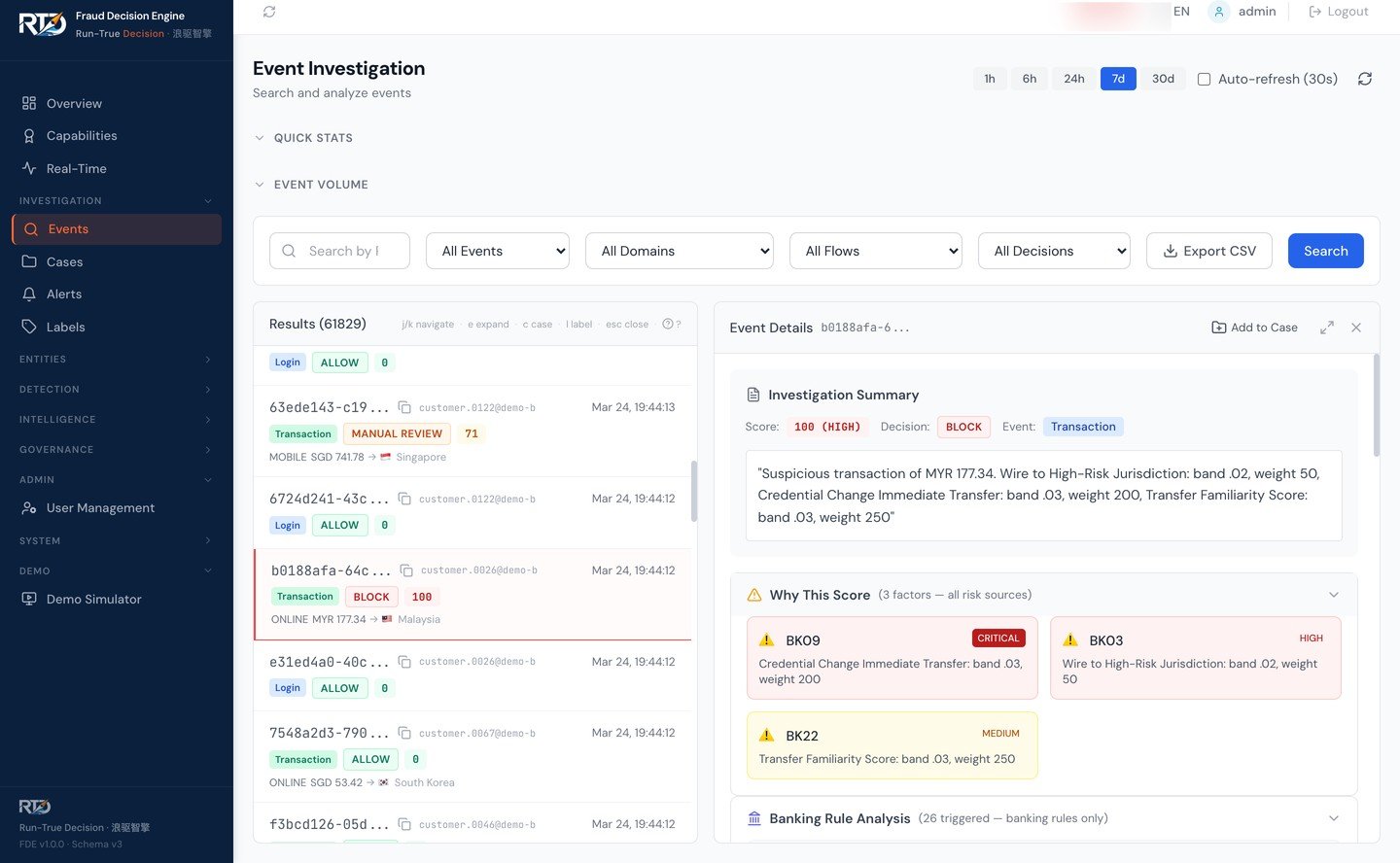
Event Investigation — drill into any transaction to see which rules fired, why the score was assigned, and connected entities.
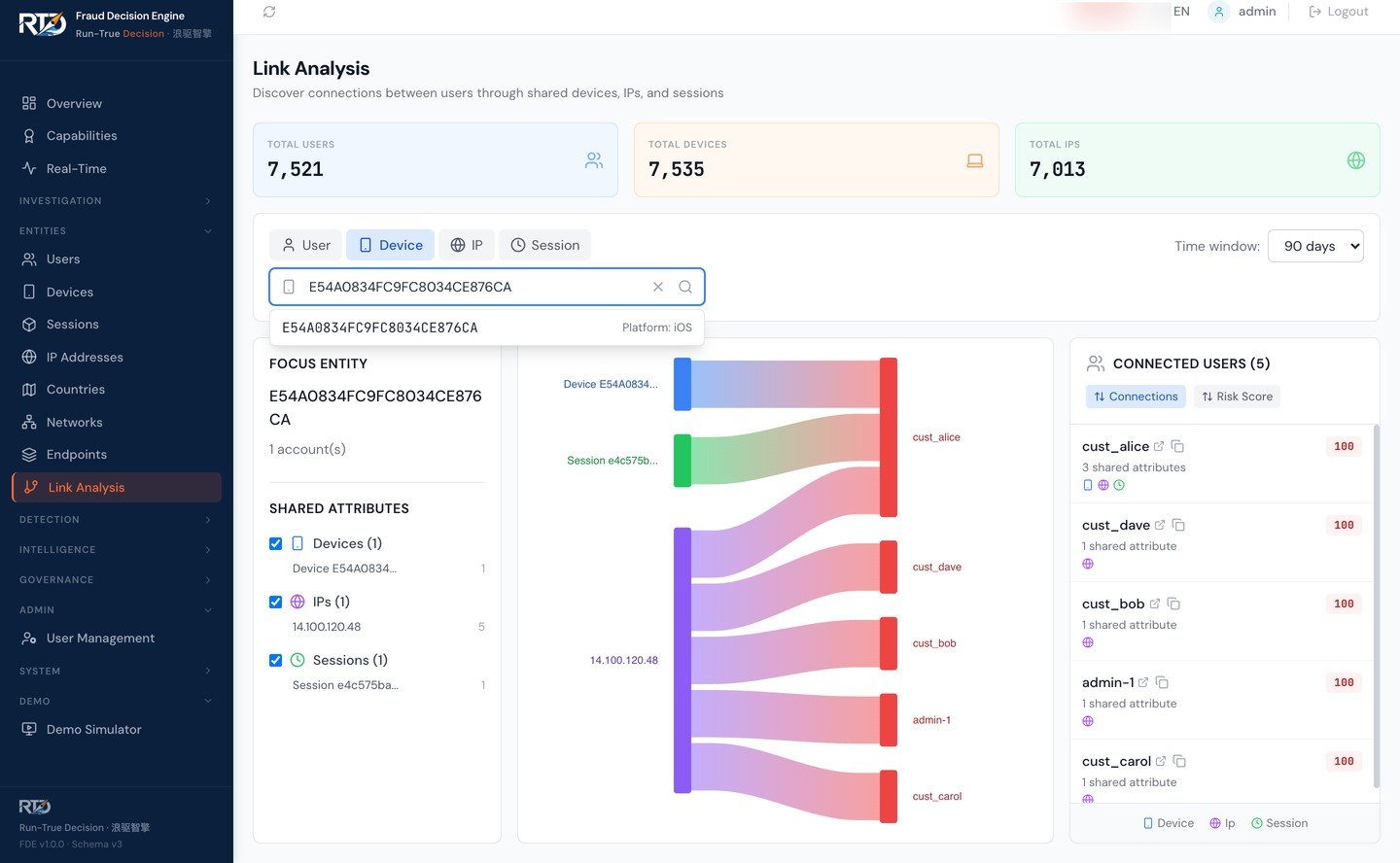
Entity Link Analysis — trace connections between devices, sessions, IPs, and users to uncover fraud rings.
Investigation Dashboard
A purpose-built interface for fraud analysts. Drill into any transaction to see exactly which rules fired, why the risk score was assigned, and how entities are connected.
- 20+ pre-built analytical views
- Role-based access control (RBAC)
- Real-time transaction monitoring
- Entity link analysis across transactions
- Customizable dashboards per analyst role
AI-Powered Investigation — From Hours to Seconds
LLM-generated summaries and conversational Q&A turn an enabled fraud event into an instantly understandable narrative — on demand for deployments with AI investigation switched on. No more digging through raw rule logs.
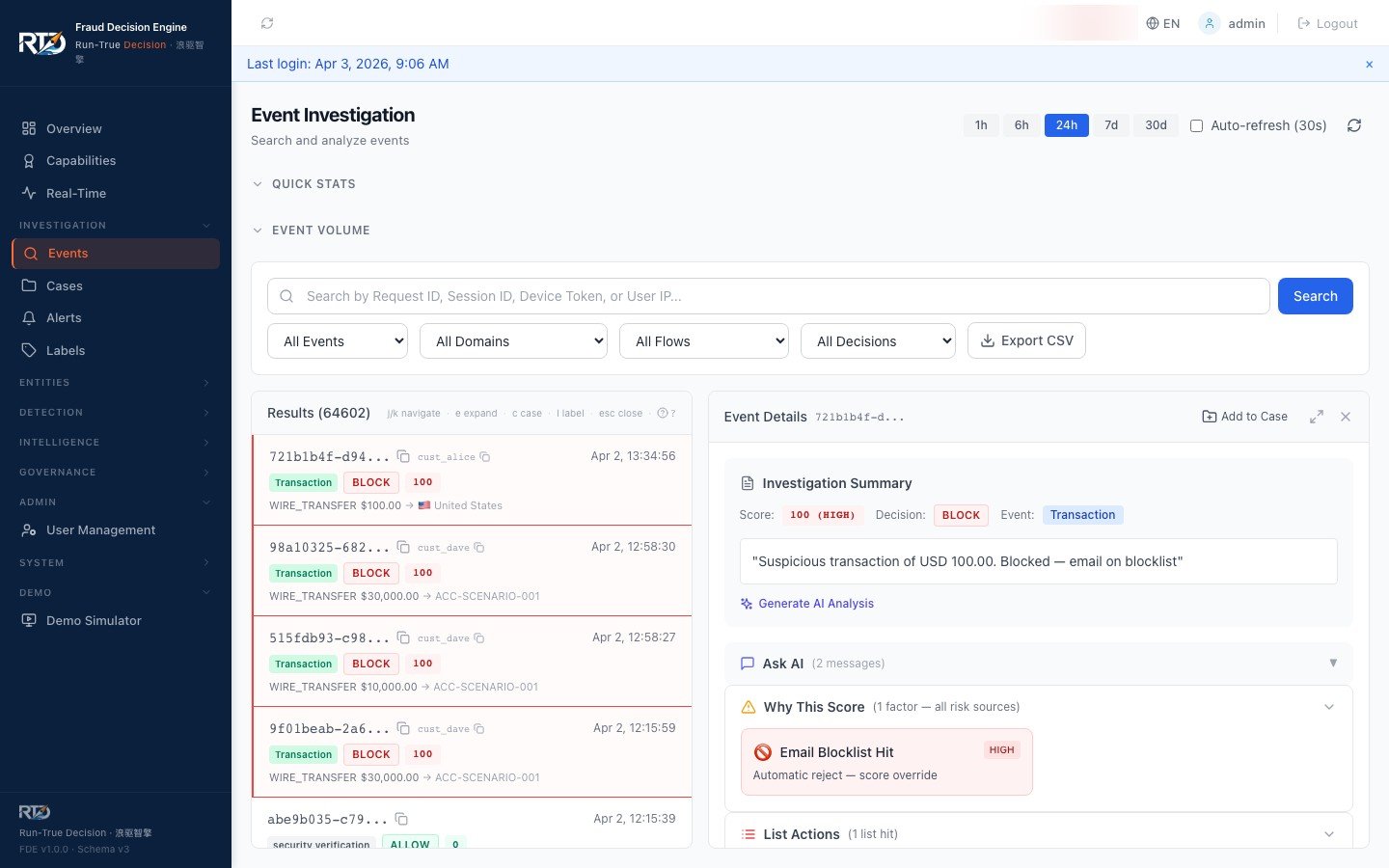
One-Click AI Summary — instant narrative for every flagged event
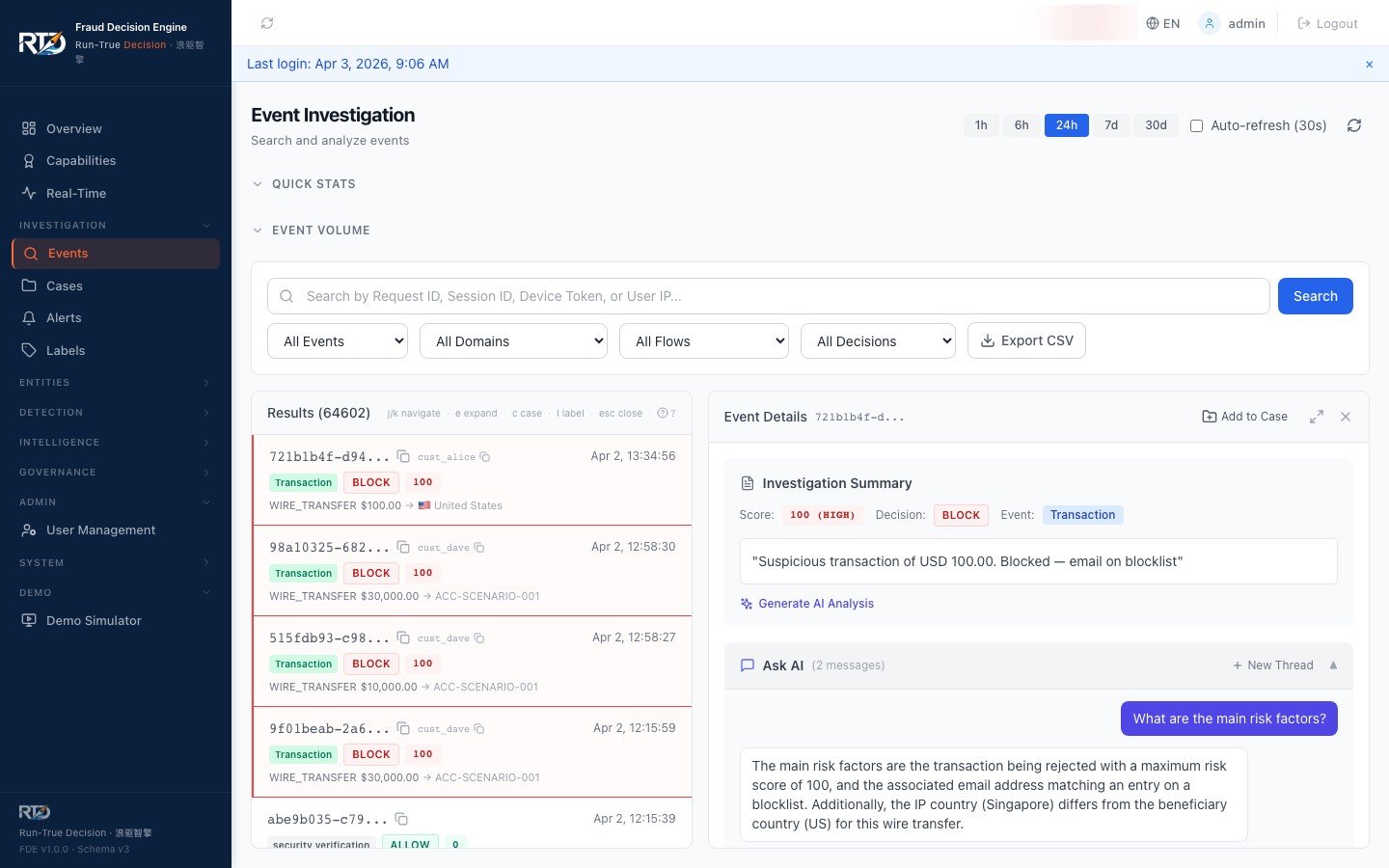
Conversational Q&A — ask "Is this a false positive?" and get grounded answers
One-Click Summary
LLM-generated narrative explaining rule triggers, risk signals, and transaction context
Conversational Q&A
Multi-turn chat with contextual, grounded answers about any fraud event
PII-Safe by Design
Direct identifiers are stripped before external LLM calls. Deployments can keep AI investigation disabled or configure provider access per policy — including strict on-prem data-residency setups.
Investigate Fraud from Anywhere
Our dashboard is fully responsive — monitor alerts, investigate events, and manage cases from your phone.
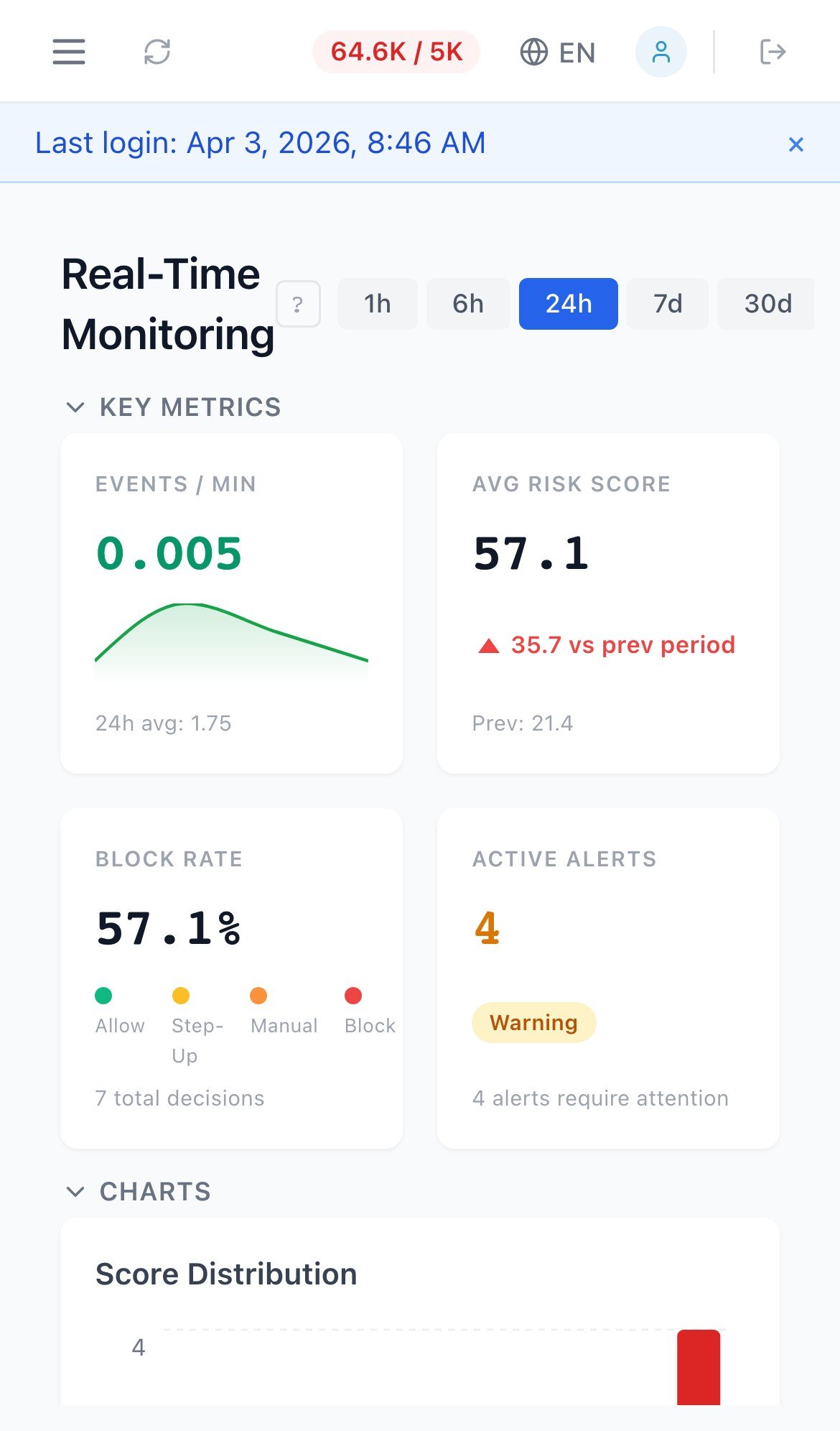
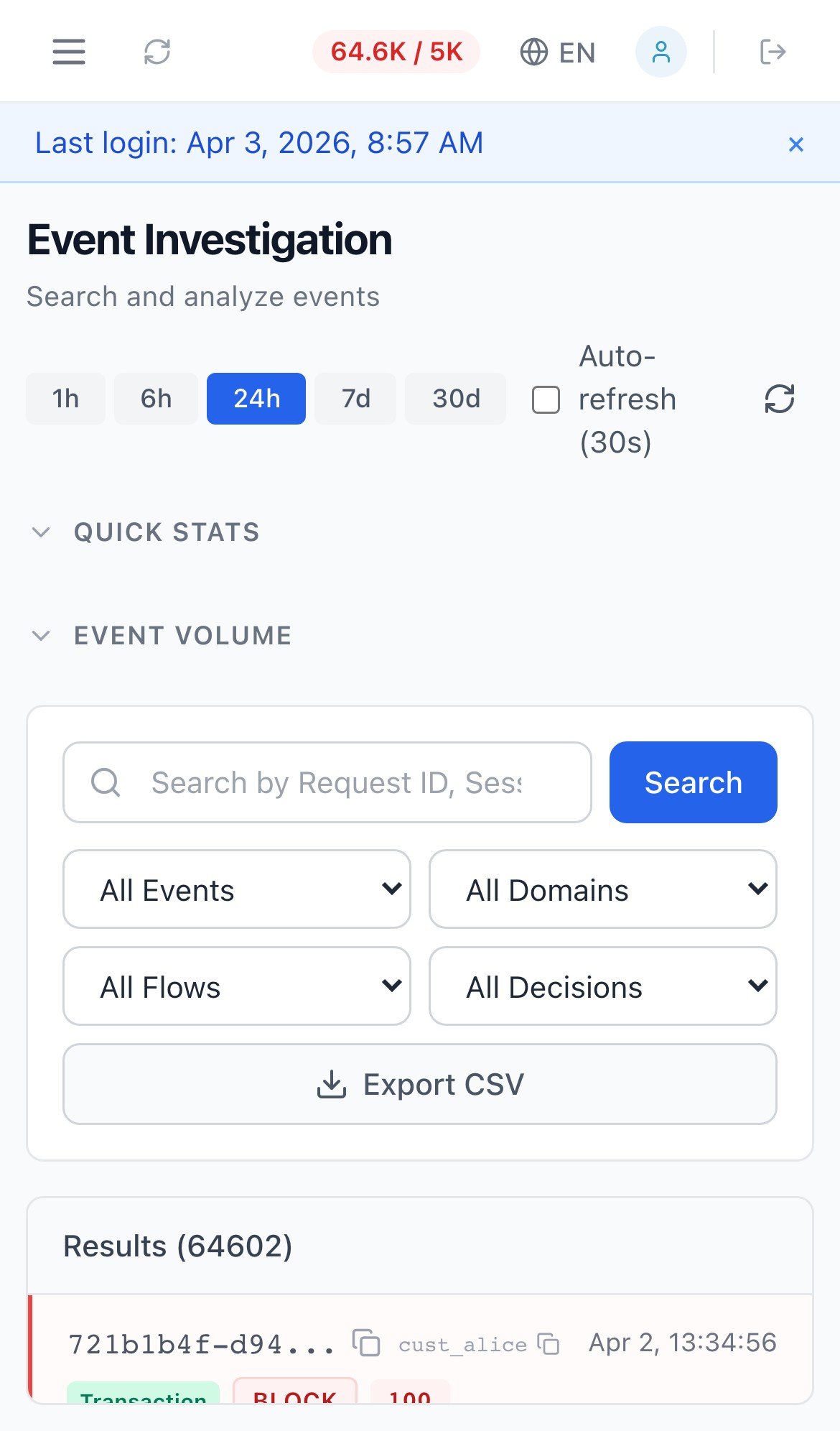
Real-Time Monitoring & Event Investigation — iPhone and Android
One Dashboard, Every Language
Every label, menu, and status in your team's language. Fraud analysts in Bangkok see the same data as analysts in Jakarta — each in their native language.
English
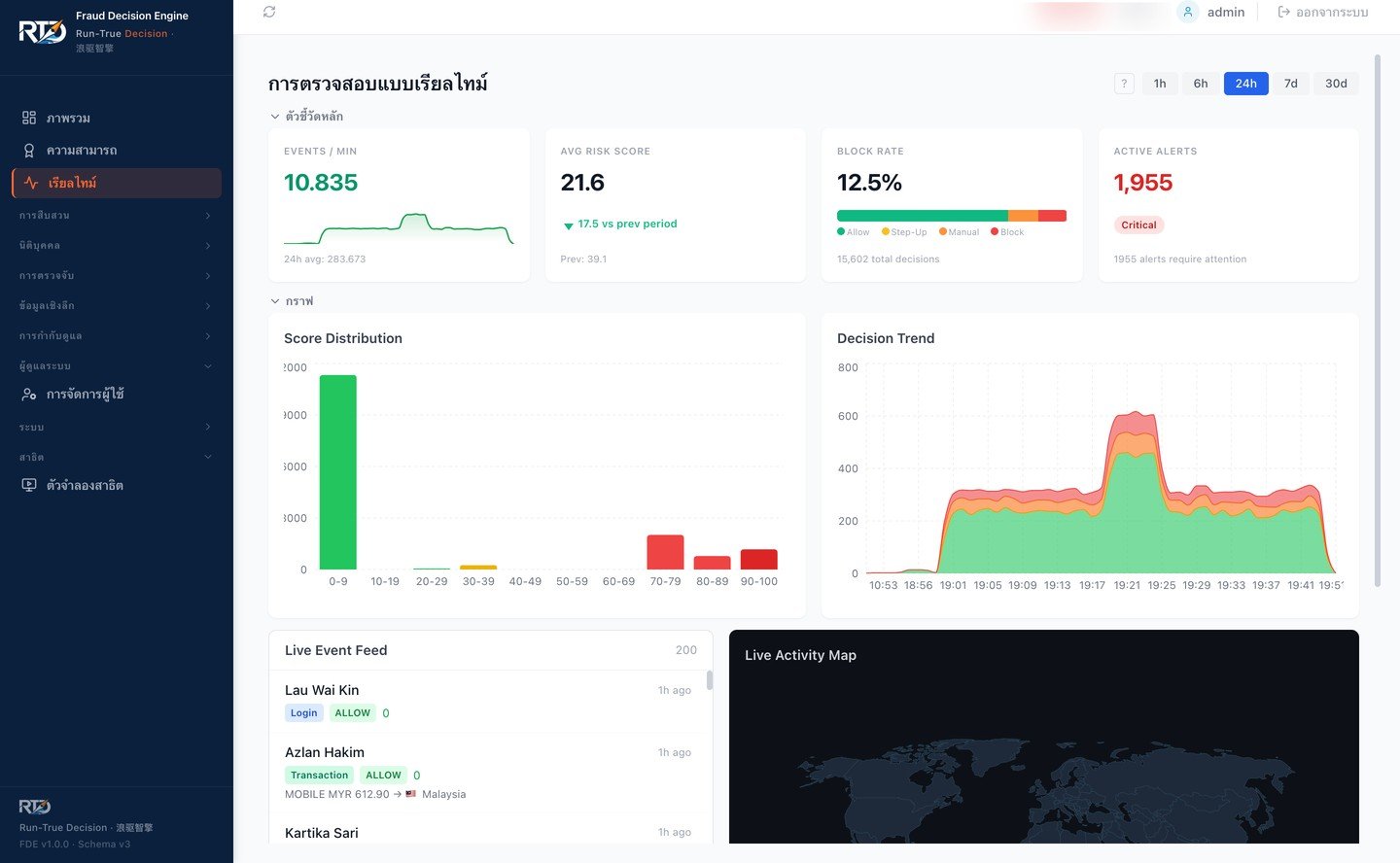
Thai
Currently supported: English, Thai, Bahasa Indonesia, Vietnamese, Chinese (Simplified). Additional languages on request.
Case Management
End-to-end case lifecycle management from alert creation through resolution, with full audit trails and compliance-ready exports.
- Full case lifecycle management
- Event linking across related transactions
- Status workflows with SLA tracking
- PII-redacted export for compliance reporting
- Team assignment and escalation workflows
Case #FRD-2026-0847
Rule change approved
Maker-checker: 2/2 approvals
AES-256-GCM encryption
Data at rest · Active
Audit log exported
Q1 2026 · 12,847 entries
Governance & Compliance
Built-in governance controls that help regulated institutions meet audit and compliance requirements without slowing down operations.
- Maker-checker enforced by code — self-approval blocked at the API, not just by policy (see how it works)
- Complete audit logging of all actions
- AES-256-GCM encryption at rest
- End-to-end TLS 1.3 with mutual authentication on every internal hop (engine ↔ nginx, engine → PostgreSQL, engine → Redis, dashboard → engine)
- TLS audit evidence — PostgreSQL emits per-connection TLS audit events with version/cipher/verified status; Redis emits TLS verification evidence at startup and reconnect (redis-py does not expose per-socket SSL metadata). Exportable jq queries map to FFIEC CAT, MAS TRM §10, and BNM RMiT §11 audit asks.
- Designed to support data residency requirements
- Role-based permissions with granular controls
- Multi-tenant deployment — isolated rule sets, auth policies, and data per brand or subsidiary
- Regulatory compliance mapping — link rules to MAS TRM, OJK, and BSP requirements; export coverage reports for auditors
Device Intelligence
Identify and track devices across sessions with deep fingerprinting that detects emulators, tampering, and suspicious device patterns.
- Device fingerprinting across web and mobile
- 47 device intelligence signals across 4 categories
- Browser and app integrity checks
- Device reputation scoring
- Cross-session device linking
- Behavioral biometrics integration — plug in your existing provider for bot detection, device tampering, and suspect scoring
Device Profile
Lists & External Feeds
Centralized list management with real-time matching during decisioning. Import your own lists or connect third-party threat intelligence feeds.
- Managed blocklists and allowlists
- CSV bulk import for fast onboarding
- Approval workflows for list changes
- Third-party threat intelligence feed integration
- Real-time list matching in decisioning pipeline
Integration & SDKs
Everything you need to integrate the Fraud Decision Engine into your existing stack.
REST API
OpenAPI spec included
TypeScript SDK
npm package
Python SDK
pip package
WebSocket
Real-time events
# Replace with your FDE instance URL after onboarding
curl -X POST https://your-instance.run-true.com/v1/risk/evaluate \
-H "Authorization: Bearer $API_KEY" \
-H "Content-Type: application/json" \
-d '{"eventCode": "payment", "sessionId": "sess_001", "deviceToken": "v2:abc123",
"eventDetail": {"Payment": {"Amount": 5000, "Currency": "SGD"}}}'Native MCP Integration
Among the first fraud engines with native Model Context Protocol support. AI assistants — Claude, GPT, Gemini — can evaluate risk, submit outcomes, and label fraud through the MCP server once configured with RTD credentials and approved tool access.
evaluate_risk
Real-time scoring with SHAP explanation
submit_outcome
Payment success/failure feedback loop
submit_fraud_label
Label events with multi-source tracking
check_health
Service availability verification
Open standard (Linux Foundation). Stdio for development, HTTP for production. Your AI agents become fraud analysts.
Deployment Options
Choose the deployment model that fits your institution's requirements. Core decisioning capabilities stay consistent across deployment models; some optional integrations (AI features, GeoIP refresh) depend on your environment configuration.
| Feature | SaaS | On-Premise Docker Compose Limited Availability · Pilot |
On-Premise Ansible / bare-metal Limited Availability · Pilot |
|---|---|---|---|
| Data location | RTD-managed cloud | Your infrastructure | Your infrastructure |
| Runtime | Containerized | Docker Compose v2 | systemd + uvicorn (no Docker required) |
| Maintenance | Fully managed by RTD | Your team, RTD-supported | Your team, RTD-supported |
| Data sovereignty | Regional hosting available | Complete control | Complete control |
| Full-mesh mTLS | N/A (TLS at edge) |
Optional ( gen-certs.sh) |
Optional ( fde_tls_internal: true) |
| Bring-your-own bank PKI (Customer CA mode in technical docs) |
N/A | Yes | Yes |
| Go-live target | 2–4 weeks | 1–3 months | 1–3 months |
| Best for | Fast deployment, fintechs | Banks evaluating, mid-market | Tier-1 banks, RHEL shops, zero-trust |
On-premise deployment designed to support data residency requirements under MAS TRM Guidelines, OJK regulations, and similar frameworks.
Managed SaaS Architecture for Real-Time Decisions
RTD SaaS gives banks a managed Fraud Decision Engine without asking their teams to operate the decision infrastructure themselves. Payment systems call the Decision API, RTD evaluates the transaction through the same governed decision workflow, and the bank receives an inline outcome with audit evidence available for review.
A clear path from transaction event to decision
The SaaS model is designed for teams that want faster deployment, managed operations, and a clear path from transaction event to decision, case review, and evidence export. The bank integrates through a decision API instead of operating the runtime.
- ·RTD manages the engine, dashboard, deployment, monitoring, backup, and restore operations for the hosted service.
- ·Decision evidence stays attached to each outcome so fraud teams can explain why a payment was allowed, stepped up, reviewed, or blocked.
- ·Tenant-level controls keep customer configuration, decision records, and operational evidence separated.
- ·Performance is validated with signed synthetic traffic before buyer-facing latency claims are made.
- ·Bank payment channels
- ·Core banking & payment switch
- ·Fraud operations users
- ·Decision API
- ·Fraud Decision Engine
- ·Tenant-separated audit & evidence layer
- ·Analyst & supervisor dashboard
- ·Monitoring & evidence exports
Managed decision infrastructure
RTD operates the engine, dashboard, monitoring, backup, restore, and deployment controls for the hosted environment.
API-first integration
Banks send transaction events to the Decision API and receive an inline outcome for payment authorization, step-up, review, or block workflows.
Tenant-separated evidence
Decision records, rules, model outputs, and investigation context are kept as tenant-separated evidence for review and audit workflows.
Measured performance
Hosted decision-path latency is benchmarked with signed synthetic traffic and published only with clear environment and claim boundaries.
Hosted production-shape benchmark — May 2026
Signed synthetic /v1/risk/evaluate workload against the hosted RTD decision path. Not a universal SLA. Customer-specific results depend on region, network path, payload shape, tenant configuration, rule mix, deployment controls, and infrastructure sizing.
Measured server decision path at c=20: p50 145 ms, p95 508 ms. Client-observed numbers are used in the headline because they reflect what a calling system sees end-to-end.
May 2026 hosted production-shape validation using signed synthetic /v1/risk/evaluate traffic. Results are not a universal SLA. Actual customer latency depends on region, network path, payload shape, tenant configuration, rule mix, and operating controls. Customer-specific commitments should be validated in the target environment.
Review the SaaS deployment path
RTD can walk your risk, technology, and compliance teams through the hosted decision path, benchmark evidence, deployment controls, and data-handling requirements before a pilot.
Request a SaaS architecture reviewOn-Prem Architecture — Built for Banking Infrastructure
For banks that need data residency, local operations, and full control over the decision plane, FDE runs inside bank-controlled infrastructure as a first-class deployment — with its own validated topology, performance profile, and security posture. The same governed decision workflow used in the SaaS model runs here, on hardware the bank operates.
Two install paths, TLS 1.3 + mTLS opt-in on both
Docker Compose deploys the 5-service stack (engine, dashboard, PostgreSQL, Redis, nginx) on a single host.
Ansible bare-metal supports a 2-VM split (app VM + dedicated PostgreSQL VM) — the topology validated in the RTD internal 2-VM reference lab. Both paths support TLS 1.3 + mTLS opt-in (fde_tls_internal: true), audit logging, and Mode A / Mode B cert flow.
RHEL / Rocky Linux 8/9 TLS caveat (current release): Redis TLS is deferred, engine + dashboard must be co-located on the same VM, and the cert chain is 7 leaves (not 9). Full 9-leaf TLS posture is available on Ubuntu 22.04 + Debian 12. On the Ansible bare-metal path: nginx is auto-installed and load-balances across uvicorn workers; Redis is co-located on the app VM for sub-millisecond list-cache lookups.
Validated performance — banking tenant
Pre-configured banking fraud detection templates (full chain enabled), RTD internal lab, Intel Xeon E3-1245 v5. Lab measurements only — not a performance guarantee. Your hardware, network, tenant config, and rule mix will affect results.
Zero errors across ~30,500 banking evaluate requests (~13,500 Docker Compose TLS + ~10,000 Ansible 2-VM plain + ~8,500 Ansible 2-VM TLS).
Zero-trust security (opt-in fde_tls_internal: true)
- ·TLS 1.3 only, AEAD ciphers, EC P-384 CA / EC P-256 leaves.
- ·Mutual TLS on every internal hop — engine ↔ nginx, engine → PostgreSQL (
sslmode=verify-full), engine → Redis, dashboard → engine. - ·Two PKI modes: RTD-generated CA (Mode A, fast PoC) or Bring-your-own bank PKI (Customer CA mode in technical docs) — validated bundle handoff.
- ·PostgreSQL per-connection TLS audit log; Redis TLS verification evidence at startup and reconnect; ready-to-paste jq queries for auditors.
- ·Cert expiry monitor runs as a systemd timer (warns at 60 days, errors at 14 days). Rotation is operator-triggered and mode-specific: Mode A reruns
ansible-playbook --tags common,tls-rotate; Mode B banks reissue their bundle and operator reruns--tags common,tls. Reload-not-restart where supported.
Compatibility
Ubuntu 22.04 (primary, CI-verified); Ubuntu 20.04 (legacy, supported); RHEL / Rocky Linux 8/9 (supported — current release TLS reduced scope: Redis TLS deferred, engine + dashboard co-located on same VM, 7-leaf cert chain). Full 9-leaf TLS posture available on Ubuntu 22.04 + Debian 12. PostgreSQL 16 verified; PG 15 supported (not yet verified); PG 14 expected. Docker Engine 24+ for Compose path; Ansible 2.14+ with Python 3.11 for bare-metal path.
Built for Banking
Pre-configured banking fraud templates across 10 category groups — from wire and ACH to behavioral biometrics. Designed against real bank RFI/RFP requirements from across Southeast Asia.
Wire Fraud
High-value transfer rules
ACH Fraud
Batch payment monitoring
Check Fraud
Deposit & clearing rules
Account Takeover
Login anomaly detection
Card / CNP
Transaction fraud rules
Money Flow
Structuring detection
Identity / Synthetic
KYC fraud rules
Cross-cut
Pattern analysis
Device Intelligence
Device-linked signals
Behavioral Biometrics
Bot & tampering detection
Transparent Pricing for Mid-Market Banks
We believe mid-market banks shouldn’t pay enterprise-tier prices for enterprise-grade fraud protection. Our pricing is designed to be accessible — talk to us for details.
Talk to Us About PricingSee It in Action
Our live demo bank at rtd-demo-bank.run-true.com connects directly to the Fraud Decision Engine sandbox. Submit test transactions, trigger rules, and see real-time scoring — no setup required.
Demo access is manually approved during our early access program.
Request Demo AccessReady to Stop Fraud Before It Moves?
Talk to our team about fraud decisioning for your institution.